The Architectural Brief for the Company of One.
Every Tuesday, I distribute the exact operational blueprints and enterprise infrastructure required to decouple your revenue from your labor hours.
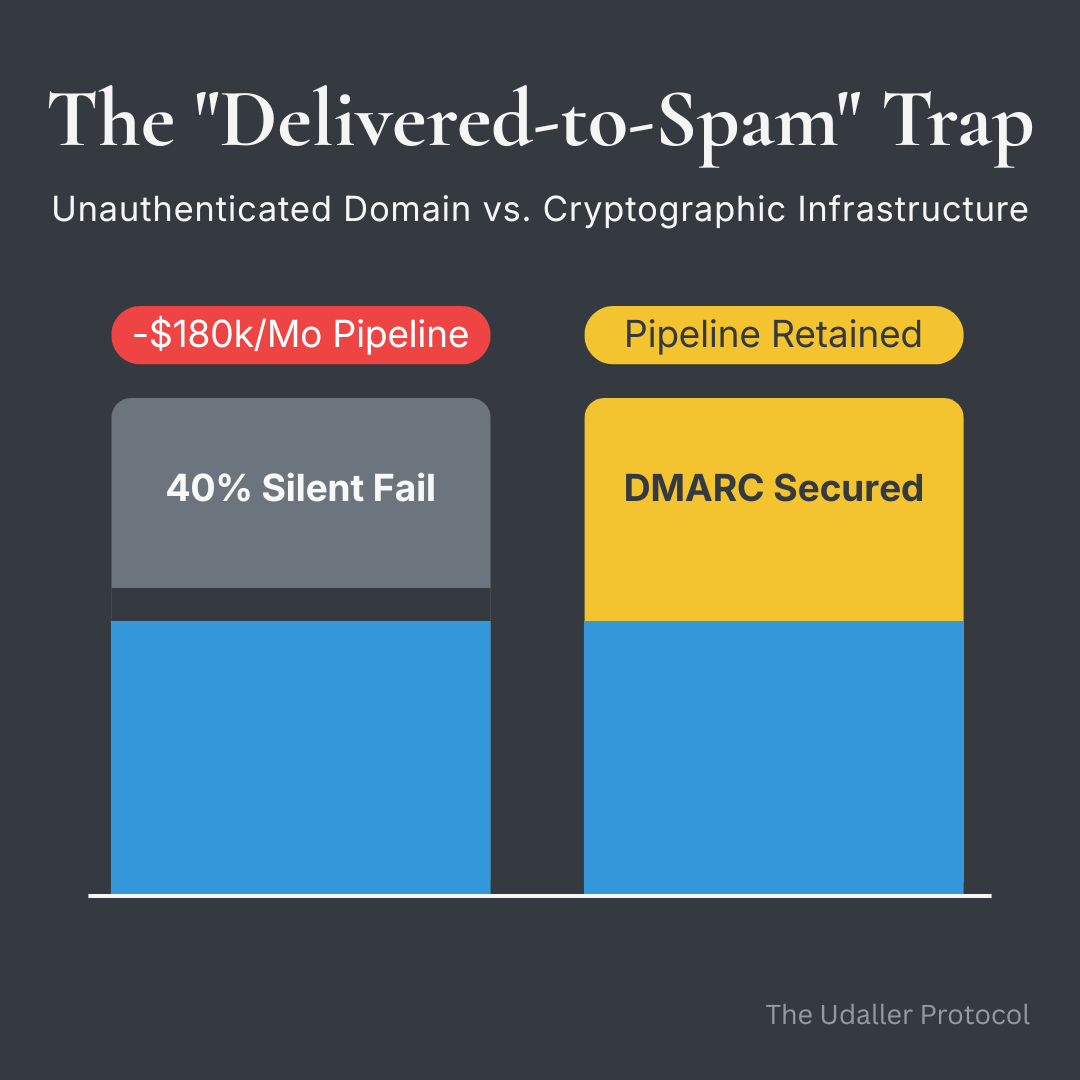
EXECUTIVE BRIEFING: This edition of the Udaller Protocol diagnoses a critical infrastructure failure affecting high-revenue solopreneurs and micro-agency operators running cold outreach campaigns. The "Silent Fail" epidemic occurs when domains lacking proper SPF, DKIM, and DMARC DNS authentication records trigger spam-folder routing by Google and Yahoo mail servers—while the sender's CRM dashboard falsely registers a 99% "Delivered" rate. Following strict 2024–2026 provider enforcement mandates, domains without proper DMARC policy and 2048-bit DKIM alignment suffer an average 40% silent fail rate. For operators with a $15,000 Average Contract Value and 1,000 monthly outreach attempts, this translates to an annualized pipeline loss of $2,160,000. The fix is not copywriting optimization—it is a DNS authentication audit. This edition maps the failure mode, quantifies the financial bleed, and deploys a diagnostic infrastructure tool called the Outreach Auditor to close the gap.
Your CRM Is Gaslighting You
Here's what you believe right now: if your CRM says an email was "Delivered," your prospect had a chance to read it.
That belief is the most expensive assumption in your tech stack.
The "Delivered" status in virtually every outreach platform—Apollo, Instantly, Smartlead, take your pick—records a single event: an SMTP 250 OK handshake. That's the receiving server saying, "Message received at the door." It tells you nothing—absolutely nothing—about what happens next. And what happens next, for a significant portion of operators running unauthenticated domains, is a silent catastrophe.
Because of strict enforcement mandates rolled out by Google and Yahoo starting in 2024, receiving servers don't bounce unauthenticated mail anymore. They don't reject it. They accept it gracefully at the handshake, then route it directly to spam—and they don't tell you. Your dashboard reads 99% delivered. Your prospect's spam folder just got a little heavier.
You've been screaming into a soundproof room and reading the echo as applause.
This isn't a marketing problem. It's a cryptographic failure—a structural blind spot in your outreach infrastructure that better subject lines will never fix.
[ SYSTEM NOTE ] Unauthenticated email domains generate a measurable revenue bleed calculated from silent fail rates applied to outbound conversion volume and average contract value. At a 40% silent fail rate against a $15,000 ACV pipeline, annualized losses reach $2,160,000 for operators sending 1,000 monthly outreach emails at 3% conversion.
I had Sage—my AI research analyst—pull the exact data on the hidden financial bleed of unauthenticated email infrastructure. Here's what the numbers actually look like:
Sage: Analysis
The Inbox Penalty: Following 2024–2026 enforcement by Google and Yahoo Postmaster, domains operating without a strict DMARC policy and 2048-bit DKIM alignment report an average silent fail rate of 40%. Mail is accepted by receiving servers at the SMTP layer and routed to spam. The sender's platform logs the attempt as "Delivered." No bounce is generated. No alert is triggered.
The Latency Tax Calculation: For a micro-agency operating at a $15,000 Average Contract Value with a 3% outbound conversion rate sending 1,000 emails per month, a 40% silent fail rate removes 400 attempts from the effective outreach pool entirely. Effective monthly sends drop from 1,000 to 600. Projected monthly pipeline drops from $450,000 to $270,000—a $180,000 monthly shortfall.
The Annualized Bleed: Operating with broken DNS authentication records produces a $2,160,000 annualized revenue loss in invisible pipeline. The operator's cost basis—time, tooling, copy production—remains identical. The throughput does not.
Source: 2025/2026 State of Email Deliverability Reports; Google Postmaster Technical Guidelines.
That $2.16M isn't going to a competitor. It isn't going to a better offer. It's dissolving into spam folders without a single signal that anything went wrong.
The Midnight Rewrite That Fixes Nothing
[ SYSTEM NOTE ] Operators who misattribute silent deliverability failures to copywriting quality enter a pattern of iterative content optimization that produces no measurable improvement. The root cause—missing or misconfigured SPF, DKIM, and DMARC DNS records—is unaddressed by subject line testing, hook rewriting, or CTA rotation.
Imagine it is the end of the month. Your cold outreach numbers have stalled, and your reply rates look anemic.
If you are like most ambitious operators, your logical diagnosis—the one every copywriting course and outreach guru reinforces—is that the copy just isn't working. So, you try to fix the copy. You sit there at midnight rewriting hooks, pulling split tests on subject lines, and swapping CTAs, convinced that you are just one psychological angle away from cracking the market.
You aren't iterating toward a solution. You are optimizing a broken pipe.
The words do not matter if the screen is never seen. If you are operating without a strict DMARC policy, your SPF records aren't properly aligned, or your DKIM is configured at 1024-bit—technically present, but practically insufficient—you are mathematically guaranteed to fail against modern enforcement standards.
You lose months of strategic output not because your offer is weak, but because you haven't configured three lines of text in your DNS settings.
That is a particular kind of frustrating. There is no rejection email and no bounce. Your platform says everything went fine, so you just sit there wondering why a market that should respond to your offer is silent—and you keep blaming the one variable you can actually see and touch: the words.
The reframe that changes everything isn't about messaging. It is about infrastructure. You aren't failing because you aren't good enough. You are failing because your technical architecture is quietly rejecting your effort before a single human can evaluate it.
Plug the Leak Before You Send Another Message
You can't fix a cryptographic problem with better copywriting. That path has a ceiling, and it's the floor.
The actual fix is unglamorous: you need to know your DNS authentication status before you send another message. SPF, DKIM, and DMARC aren't optional configurations for cautious enterprise IT teams—they're the foundational layer that determines whether your outreach physically lands in a primary inbox or disappears into a void your prospect will never open.
I built a diagnostic utility specifically to debug this leak. It's called the Outreach Auditor. It's a single-file tool that pings your DNS APIs and surfaces your record status in real time.
THE EXECUTION:
Deploy this infrastructure now to see if you are paying the 40% Spam Folder Tax:
Step 1: Input your root domain (no account required).
Step 2: Review your real-time SPF, DKIM, and DMARC status.
Step 3: Apply the specific missing DNS text records to your registrar to close the authentication gap.
If your records are clean, you'll know. If they're broken or misconfigured, you'll know that too—and you'll have a specific, fixable list of what needs to go into your DNS settings to close the gap.
This isn't an optimization play. It's a perimeter audit. You're finding out whether your outreach infrastructure is actually intact, or whether you've been operating with a silent leak in the foundation while attributing the revenue bleed to everything else.
Run the audit. Fix what it surfaces. Then deploy your sequences knowing your architecture is actually doing the job you're paying for.
— Scott
Stop Subsidizing Your Business With Your Own Time.
Don’t just scale. Build a machine. Access the private repository of offline remediation blueprints and enterprise-grade infrastructure designed to plug your revenue leaks.
